In This Article
As the crypto industry matures in 2026, cryptocurrencies are no longer niche investments; they are core parts of personal portfolios, business treasuries, and global finance. However, with mainstream adoption comes increased risk. Whether you’re holding Bitcoin, Ethereum, or the latest memecoin, securing your cryptocurrency wallet has never been more critical.
Hackers, phishing attacks, and wallet scams continue to evolve, making it essential to understand how to keep your cryptocurrency safe. From cold wallets to seed phrase backups, knowing how to keep your crypto wallet safe is a basic requirement for anyone serious about cryptocurrency and Web3.
In this guide, we’ll walk you through the best crypto wallet security tips for 2026, from selecting a secure wallet to protecting your private keys and avoiding common mistakes. If you’re wondering how to keep your cryptocurrency safe in today’s high-stakes environment, this article has you covered.
Key Takeaways
- Crypto wallet security is essential – Understanding how to properly store your crypto is critical for protecting your digital assets.
- Wallets store keys, not coins – Digital wallets don’t hold actual coins, they store your keys, which control access to your funds. Losing your private key (or seed phrase) means losing your crypto.
- Backups and cold storage matter – Create offline backups of your wallets, ideally using metal seed phrase protectors or secure hardware wallets for long-term storage.
- Advanced threats are evolving – From phishing and clipboard hijackers to SIM swap attacks and fake wallet apps, wallet-related scams are increasingly becoming sophisticated.
- Have a recovery plan – If you suspect a breach, immediately transfer your funds to a new wallet, revoke suspicious permissions, and change all associated credentials.
Crypto Wallet Security: Summary
You’ve been hodling your Bitcoin for years, improving your crypto trading, and timing market moves perfectly. Finally, you’ve built up a fortune in crypto gains and are ready to cash out and upgrade your lifestyle. One fine day, you open up your crypto wallet, check your balance… and wow, you see nothing but dust.
This is the exact scenario that you want to avoid; we will teach you how to prevent it in this article. Your cryptocurrency wallet security is paramount, and it can be tough to learn. However, it’s essential to know how to secure crypto properly. In this guide, we’ve compiled a ton of tips through research and, more importantly, through years of experience. So, sit back, relax and keep reading.
What Is Crypto Wallet Security?
Cryptocurrency wallet security refers to the protection measures used to keep your crypto and NFTs safe from scammers, hackers, and thieves. It involves safeguarding your private keys, the critical pieces of information that prove ownership of your crypto, and ensuring that your digital wallet is resistant to hacks, malware, and phishing scams. Whether you’re storing Bitcoin, Ethereum, NFTs, or other digital assets, understanding how to keep your crypto wallet safe is essential.

Wallet security is one of the most important parts of crypto investing. Unlike traditional bank accounts, cryptocurrency wallets are decentralized, meaning there is no customer service line to call if your funds are stolen or lost. There is no FDIC insurance on the Bitcoin sitting in your cold wallet, meaning that you are the only line of defense.
That makes personal responsibility and strong wallet security absolutely vital. Choosing the best crypto wallet security practices, like using a hardware wallet, enabling two-factor authentication, and backing up your seed phrase, can mean the difference between long-term success and permanent loss.
It’s also important to understand the difference between wallet security and exchange security. When you store crypto on a centralized exchange, your private keys are held by that platform, making you vulnerable if the exchange is hacked or shut down. A secure crypto wallet, especially a non-custodial wallet like Best Wallet, puts the control back in your hands, so you can truly own your cryptocurrency.
Understanding How Crypto Wallets Work
To truly understand wallet security, it’s important to first understand how crypto wallets work. A common misconception is that a wallet stores your cryptocurrency, like a physical wallet stores cash. In reality, a crypto wallet doesn’t hold coins, it holds your private keys, which give you access to your coins on the blockchain. These keys are what allow you to manage and transfer your crypto securely.
Each wallet has a pair of cryptographic keys: a public key and a private key. The public key is used to generate your wallet address, which you can safely share to receive funds. The private key, however, must be kept secret. In fact, securing your private keys is the most important thing you can do to protect your crypto. It’s used to sign transactions and prove that you own the assets associated with your wallet. If someone gains access to your private key, they can move your funds, no questions asked.

When you send crypto, your wallet uses the private key to sign the transaction. That signed message is then broadcast to the blockchain network, where other nodes verify it using your public key. If everything checks out, the transaction is confirmed and added to the blockchain.
Because your private key is so important, backing up your wallet is critical. Most wallets generate a seed phrase, a list of 12 or 24 words that can be used to recover your private keys. Losing access to your private key or seed phrase usually means losing your funds permanently. That’s why keeping a secure, offline backup (and storing it in a safe place) is one of the most important steps in keeping your crypto wallet safe. You may even want to look into seed phrase backup tools, like the Cryptotag. Check out our Cryptotag Review: Comparing Loki and Zeus for more details.
Types of Crypto Wallets and Their Security Risks
When it comes to crypto wallet security, understanding the different types of wallets, and the risks they carry, is essential. Each wallet type offers varying levels of protection and convenience, and knowing how to keep your crypto wallet safe begins with selecting the right one for your needs. Below is a breakdown of common wallet types, their vulnerabilities, and what recent hacks like the one with Bybit teach us about best crypto wallet security practices.
Hot Wallets (Software Wallets)
Hot wallets include mobile wallets, desktop wallets, and web-based wallets. These wallets are connected to the internet, making them convenient for frequent use and trading. However, their online accessibility also exposes them to a range of threats such as phishing attacks, malware, keylogging, and clipboard hijacking.
One notable example is the Bybit security breach in 2023, where hackers exploited user session hijacking vulnerabilities. This highlighted the importance of multi-factor authentication and never storing large amounts of crypto in software wallets unless absolutely necessary.
Cold Wallets (Hardware and Paper Wallets)
Cold wallets are considered the gold standard for crypto wallet security. These wallets are offline and include hardware wallets (like Ledger and Trezor) and paper wallets. Because they are not connected to the internet, they are largely immune to most online hacks and risks.

Still, cold wallets aren’t foolproof. Hardware wallets can be compromised if purchased from unofficial sources, while paper wallets are susceptible to physical damage, theft, or loss. Secure storage of these wallets is crucial. Whether that means using a fireproof safe or a trusted seed phrase protector like Cryptotag.
Cryptocurrency stored offline is typically safer than keeping your crypto in a hot wallet, however it requires a lot of personal responsibility to custody your own crypto. Understanding the different types of crypto wallets and how to protect them is a foundational step in learning how to keep your cryptocurrency safe. Always evaluate your use case, daily trading vs. long-term holding, and pick the right wallet accordingly.
Hot Wallets vs. Cold Wallets – Which Is Better For Security?
Here’s a quick comparison for you to figure out which one is better for you
|
Feature |
Hot Wallets |
Cold Wallets |
|
Connectivity |
Always connected to the internet |
Kept offline until use |
|
Convenience |
High. Easy for frequent transactions |
Low. Less convenient for daily use |
|
Security Risk |
Higher. Vulnerable to online threats |
Lower. Protected from online hacks |
|
Best Use Case |
Active trading, small balances |
Long-term holding, large balances |
|
Examples |
Mobile apps, browser wallets |
Hardware wallets, paper wallets |
How to Store Crypto Safely in 2026?
The tools and ways people have used to secure their crypto has changed drastically over the years. The tech changes all the time, and people have evolved from storing Bitcoin in paper wallets to using a plethora of tools for mobile devices and desktops alike. Truly, crypto security, like digital security, is an ever changing topic, but thankfully we’ve compiled a list of tips you need to properly store your crypto in 2026.
Crypto Wallet Security Tips for Beginners
If you’re new to crypto, securing your wallet should be one of your top priorities. Here are a few simple but essential crypto wallet security tips to help you protect your funds:
These beginner tips can go a long way toward helping you keep your crypto wallet safe in 2026 and beyond.
Advanced Crypto Wallet Security Techniques
Once you’ve mastered the basics, leveling up your security game is essential, especially if you’re managing larger holdings or active in DeFi. Here are advanced techniques to help maximize protection:
These advanced techniques aren’t just for institutions; any serious investor can and should adopt them to future-proof their crypto security.
How to Protect Your Private Keys & Seed Phrases
Protecting your private keys and seed phrases is essential to safeguarding your crypto assets from online threats. Because this information is extremely sensitive data, your key storage method should prioritize secure storage at all times. Avoid keeping seed phrases in cloud services, email drafts, or digital notes, where they’re vulnerable to hacks, phishing, or malware.
Instead, store them offline using fire and water-resistant options like metal backups or secure hardware devices. By keeping this sensitive data out of reach from online threats and ensuring your key storage follows best practices, you significantly reduce your risk of losing access to your cryptocurrency.
Common Threats to Crypto Wallets
Understanding the most common threats to your crypto wallet is essential for protecting your cryptocurrency. As the industry grows, so does the number of cyberattacks and scams targeting both beginners and seasoned investors.

Here are some of the top threats to crypto wallet security in 2026, and how to guard against them.
By being aware of these threats and practicing good crypto security, you can dramatically reduce the risk of being hacked or scammed. Always stay updated, cautious, and skeptical, especially when it comes to your seed phrase and private keys.
How to Choose a Secure Crypto Wallet?
Here are some factors you should take into consideration while selecting a crypto wallet.
Now that you understand exactly why securing your cryptocurrency properly is so important, let’s dig in to which cryptocurrency wallet brands you should choose from.
Top 6 Secured Crypto Wallets in 2026
The following are five of our top picks for crypto wallet options with a good emphasis on security in 2026. They offer a blend of usability, good design, and fund security. These wallets are a solid mix of software wallets and hardware wallets, as many crypto users like to utilize both.
Best Wallet – Most Secure Non-Custodial Wallet of All Time
Best Wallet is a mobile-based non-custodial hot wallet built to give users a smooth, no-nonsense way to tap into Web3. It works across major chains like Ethereum, BNB Chain, Polygon, Arbitrum, and a bunch of others.

If your crypto life involves juggling tokens, browsing NFTs, jumping into crypto presales, or diving headfirst into DeFi, this wallet doesn’t make you jump through hoops to get there. As a hot wallet, Best Wallet is all about speed and simplicity. You can send, receive, and swap tokens on the fly, no browser extensions, no cables, no fiddling with hardware.
It also keeps your privacy in check. Your private keys stay on your phone, and there’s no need to hand over ID documents just to use the basics. That makes Best Wallet a great option for a secure hot wallet. The layout is clean, transactions run lean, and future updates like NFT galleries and staking tools are already on the roadmap. All in all, it’s a wallet built for people who are actually using crypto, not just holding it.
Best Wallet Key Features
- Self-Custody: You hold the keys. Literally. You’re the only one who can move your funds.
- Multi-Asset Support: Juggle a bunch of tokens from different blockchains without needing five different apps.
- Integrated Swapping: Swap tokens directly in the app, no copy-pasting wallet addresses or signing in elsewhere.
- Staking Capabilities: Stake supported coins straight from the wallet and earn while you chill, making it one of the best hot wallets for DeFi.
- User-Friendly Interface: Whether you’re brand new or a crypto vet, the layout won’t make your head spin.
- Security Measures: Built-in encryption and biometric options help keep your crypto locked down tight.
- Regular Updates: The team actively rolls out improvements, so the wallet keeps getting sharper and more useful over time.
Best Wallet Pros and Cons
Pros
-
You have full control of your private keys, which gives you peace of mind.
-
Handles a wide range of assets in one place.
-
Swapping and staking are built right in, no extra apps required.
-
The interface is clean and easy to use, no learning curve necessary.
Cons
-
No desktop version, so if you’re not a mobile person, it might feel a bit limiting.
-
Still fairly new, so some niche or power-user features might be missing (for now).
Best Wallet is a good balance between control, convenience, and everyday usability. It provides the tools you need without complicating things, and it doesn’t get in the way when all you want to do is make a quick swap or claim an airdrop. It also takes solid security precautions, making it a good choice for those who value the security of their cryptocurrency wallet.
For a full breakdown, check out our Best Wallet Review 2026.
Zengo – Popular MPC Wallet For Beginners
Zengo Wallet is another mobile-based hot wallet that ditches the old-school seed phrase in favor of something a lot more modern and a whole lot safer: Multi-Party Computation (MPC).
That alone makes it one of the more stress-free options out there. It supports big-name blockchains like Ethereum, Bitcoin, Polygon, and Solana, giving you plenty of flexibility to manage your crypto life from your phone.
What really makes Zengo pop is the mix of everyday convenience and serious security. You can send, receive, and manage crypto in real time, straight from your mobile, super handy for quick transactions or checking on things during a coffee break. And since there’s no seed phrase to remember or write down, you don’t have to worry about misplacing the one thing that could lock you out forever. Instead, your identity is tied to your face and a secure backup system that’s surprisingly easy to use.
Plus, there’s real-time customer support built into the app, which is something you rarely get with hot wallets. That alone can be a lifesaver when something feels off or you just need a quick answer.
Zengo Key Features
- MPC-Based Security: Instead of using a single recovery phrase, your wallet is secured with two separate encrypted parts, so there’s no single point of failure hanging over your head.
- 3D FaceLock Biometric Authentication: Logging in and approving transactions? Just look at your phone. It’s fast and secure, and there’s no password to forget.
- Three-Factor Recovery (3FA): If something ever happens to your phone, you can still recover your wallet using a combo of facial recognition, email, and a secure recovery file.
- Multi-Asset Support: Zengo supports more than 1,000 coins and tokens, including NFTs. So whether you’re into Bitcoin, ETH, or weird little ERC-20 tokens, you’re covered.
- Integrated Trading Features: You can buy, sell, and swap directly from the app without bouncing between different platforms.
- Zengo Pro Subscription: Unlocks some premium extras like Legacy Transfer (for passing down assets), Theft Protection, and a Web3 Firewall to help spot shady dApps before they cause trouble.
Zengo Pros and Cons
Pros
-
No more panic about losing a recovery phrase or writing it down in a sketchy spot.
-
The design is clean and easy to navigate, even if you’re new to crypto.
-
It uses some of the strongest security tech available, including MPC, biometrics, and layered recovery options.
-
Lets you manage a wide mix of coins, tokens, and NFTs in one place.
-
Adds some smart tools for people who want extra security or long-term planning options.
Cons
-
Some big names like Cardano and Polkadot aren’t supported yet.
-
You might notice trading fees sitting around 4%, which is a bit on the high side.
-
If you’re the type who prefers handling things on a laptop, this setup might feel a bit cramped.
Zengo is built for people who want solid security without dealing with the headache of seed phrases. With its modern take on key management, smooth interface, and wide support for crypto assets, it hits a sweet spot between usability and peace of mind. Sure, it has its quirks, like slightly higher fees and missing support for a few coins, but if you’re looking for a wallet that won’t leave you locked out or overwhelmed, Zengo is definitely worth checking out.
Zengo Wallet is one of the safest hot crypto wallets in 2026, check out the complete Zengo Review 2026
D’Cent Wallet – Super App with Biometric Hardware Security
D’CENT Wallet steps in with hardware-grade protection. It’s a hybrid wallet that pairs a physical device with a mobile app, giving you biometric security alongside the flexibility to manage thousands of tokens. D’CENT stands out because your fingerprint replaces passwords and seed entry, reducing phishing risks and transaction friction.
With support for 4,600+ cryptocurrencies across 85+ blockchains, including Bitcoin, Ethereum, Solana, and Polygon, it’s versatile enough for both long-term holders and active traders. The secure chip (EAL5+ certified) and offline key generation make it one of the more tamper-resistant wallets on the market, while encrypted Bluetooth syncs safely with your phone.
D’CENT Key Features
- Biometric Security: Fingerprint authentication replaces manual seed entry, making wallet access and approvals safer and faster.
- CC EAL5+ Certified Chip: Hardware-level protection keeps private keys isolated from online threats.
- Multi-Chain Support: Manage 4,600+ cryptocurrencies across 85+ blockchains, including BTC, ETH, and Solana.
- Encrypted Bluetooth Connectivity: Sync securely with your phone without exposing sensitive data.
- Mobile App Integration: Trade, swap, and manage DeFi/NFT assets directly from the companion app.
- Firmware Updates: Frequent updates ensure ongoing protection against new security risks.
D’CENT Pros and Cons
Pros
-
Biometric logins replace seed entry for safer, faster use.
-
Hardware security without losing mobile convenience.
-
Supports a broad range of coins and networks.
-
Global reputation with frequent firmware updates.
Cons
-
More expensive than simple hot wallets due to features.
-
Primarily optimized for mobile.
D’CENT fits neatly into this guide’s focus on crypto wallet security. It bridges the gap between hot and cold wallets, giving you hardware-grade safety with the ease of app-based trading. If you’re worried about scams, phishing, or simply misplacing your seed phrase, D’CENT’s biometric-first design is a smart alternative. Read more on that in our D’CENT Wallet review.
Binance Wallet – Highly-Rated Web3 Wallet
The Binance Web3 Wallet is a mobile-based, non-custodial hot wallet that lives right inside the official Binance app. It acts like your passport to DeFi, NFTs, token swaps, and early-stage launches, all without ever needing to leave the Binance cryptocurrency exchange universe.
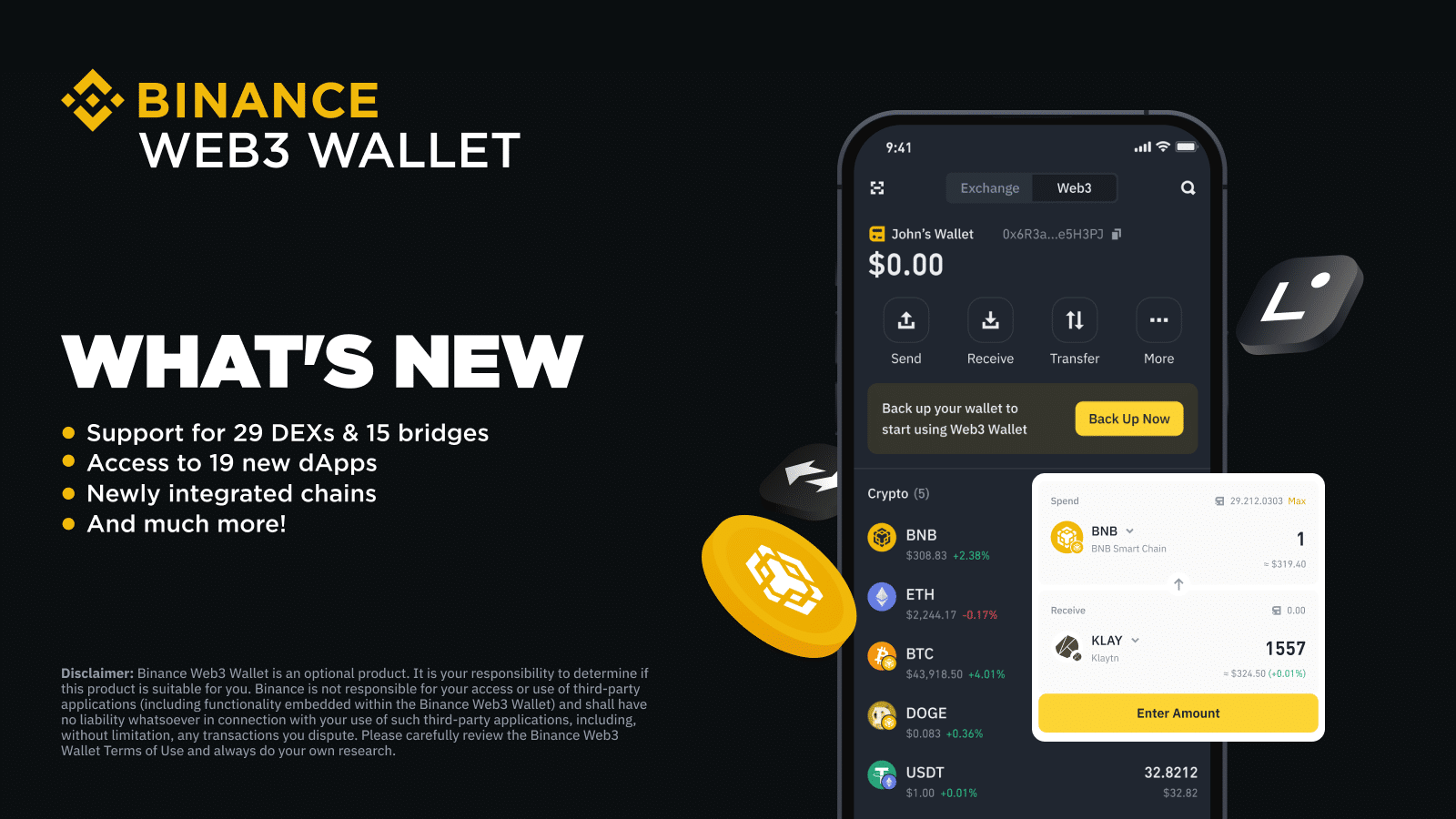
It plays nicely with a long list of blockchains, like Ethereum, BNB Chain, Arbitrum, Optimism, and Solana, so you’re not stuck in one lane.
As a hot wallet, it’s built for speed and mobility. You can jump into dApps, track your crypto, and make token swaps all from your phone. It comes with a built-in DEX aggregator to help you find the best swap rates across decentralized exchanges, and the interface is clean enough that you won’t get lost halfway through a transaction.
One thing that’s pretty slick, if you already have crypto in your Binance account, you can shift it into your Web3 Wallet in just one tap. That saves time and makes the jump from centralized to decentralized feel a lot less messy. Your private keys stay on your device, and backups are done the old-fashioned way with a seed phrase, so you’re still in control of your funds.
For security, you’ve got biometric logins, clear transaction previews, and phishing alerts baked in, all stacked on top of Binance’s own infrastructure. So you’re getting both the flexibility of DeFi and the safety net of a platform that’s been around the block.
Binance Wallet Key Features
- Integrated Multi-Chain Support: Works with over 70 blockchains, so you can store, send, and interact with assets across multiple ecosystems from one place.
- MPC-Based Security: Your private key gets split into parts behind the scenes, which adds an extra layer of protection and removes the need to write down a seed phrase.
- Unified Wallet Interface: Combines your wallets, tokens, and NFTs into one clean dashboard. No more juggling different apps to figure out what you own.
- Built-In dApp Browser: Lets you connect with DeFi protocols, explore NFT platforms, and use Web3 apps without leaving the wallet.
- Cross-Chain Token Swapping: Allows you to swap assets between different blockchains directly from the app. Rates are competitive, and you skip the usual hassle.
- Security Alerts: Warns you before you interact with sketchy contracts or send funds to a bad address. Saves you from some painful mistakes.
- Airdrop Zone and Reward Center: Dedicated sections for claiming airdrops and tracking rewards. If you like free tokens and bonus perks, this is where you’ll want to look.
Binance Wallet Pros and Cons
Pros
-
No extra downloads or setup. It’s built right into the Binance app.
-
Between MPC and biometrics, your wallet stays secure.
-
Supports a wide range of coins, tokens, and NFTs, all under one roof.
-
Staking, lending, swapping, you can do it all directly from your phone.
-
Actively improves the wallet experience, so new tools and upgrades roll out regularly.
Cons
-
You’ll need a Binance account to use it.
-
Since it’s tied to your Binance account, your activity can be monitored or flagged.
-
This wallet doesn’t currently offer a desktop option.
-
Depending on where you live, some features may not be available.
The Binance Web3 Wallet is a handy choice for anyone who wants to dive into DeFi without straying too far from the comfort of Binance. It’s packed with useful features, supports a ton of networks, and bridges the gap between CeFi and DeFi in a way that feels smooth and intuitive. Just be aware that it’s still tied to the Binance ecosystem, so if full decentralization and privacy are top priorities, you may want to look elsewhere.
For everyone else, especially Binance users, it’s a fast and capable wallet that gets the job done. Read our Binance wallet review for a complete look at how it works.
Ledger Flex – Top Hardware Wallet With Strong Security
The Ledger Flex is a sleek hardware wallet featuring crypto’s first E-link display, known for its ease of navigation and low power consumption, similar to what’s used in Amazon Kindle e-readers. Its display uses organic semiconductor materials instead of silicon and is layered on plastic substrates, a departure from the traditional silicon-on-glass.

This hardware wallet supports crypto and NFTs and uses a secure element chip to keep your private keys safe. The vision behind Ledger Flex is clear: to introduce innovative products that not only simplify the management of digital assets but also make using hardware wallets a genuinely delightful experience.
With the Ledger Flex, you can manage over 5,500 different coins and tokens. This extensive support spans major coins, exchange tokens, DeFi, meme coins, AI, GameFi, and the metaverse, among others. Use the handy search function to check if your specific coins are supported.
Beyond cryptocurrencies, this device allows you to manage and secure your NFTs on the Ethereum and Polygon blockchains via Ledger Live. It also supports several other blockchains through third-party wallets like MetaMask, Rabby, Phantom, and Electrum.
Ledger Flex Key Features
- Design & Durability: Slim, portable, and deceptively powerful, the Flex fits neatly alongside your credit cards without compromising durability. It’s the kind of wallet you can toss in your bag or pocket without a second thought. The secure touchscreen is just the cherry on top, functional, intuitive, and a dream to use.
- User Interface: The touchscreen makes entering PINs and confirming transaction details feel more like unlocking your phone than interacting with a crypto vault. It pairs effortlessly with the Ledger Live app, giving you quick and easy access to your portfolio, exchange accounts, and even NFT galleries.
- Supported Cryptocurrencies: You name it, the Flex supports it. From major coins to staking and NFT storage, this device covers over 5,500 cryptocurrencies. It’s like having a universal remote for your entire crypto empire.
- Security Features: The secure element chip is where the magic happens. It protects your private key like a bank vault, while the secret recovery phrase stays offline, where no attacks can touch it. The Flex’s security model ensures that even if someone gets hold of the device, they won’t get hold of your assets.
- Unique Features: While the touchscreen doesn’t have the fancy curved E Ink of the Stax, the Flex’s screen balances usability and simplicity, offering just enough pizzazz without overcomplicating things.
- Compatibility: Thanks to Bluetooth functionality, the Flex connects seamlessly with mobile devices and the Ledger Live mobile app. You can be on the go or chilling at home, it’s the ultimate portable option for managing your crypto.
Ledger Flex Pros and Cons
Pros
-
Slim, lightweight design with a secure touchscreen.
-
Bluetooth-enabled for mobile connectivity.
-
Supports staking, NFTs, and over 5,500 cryptocurrencies.
-
Top-notch security with a secure element chip.
-
Pairs seamlessly with the Ledger Live app.
Cons
-
Closed-source software may deter open-source advocates.
-
No wireless charging.
As a physical device, a hardware wallet provides a high level of security by keeping your private key isolated in a secure chip. It is the chip stored within the device itself that makes these wallets stand out. However, not all chips are the same, and Ledger here utilizes a Secure Element, a special computer chip commonly used in bank cards, credit cards, and passports.
Secure Element chips undergo third-party testing for certification, which is a crucial part of their security model. Rated as per the Common Criteria (CC) Evaluation Assurance Level (EAL) standard, Ledger’s Secure Element in the Flex is EAL6+ certified. This scale, which goes up to EAL7+, makes this Ledger hardware wallet extremely secure.
Trezor Safe 5 – Most Popular Hardware Wallet
The Trezor Safe 5 is the latest flagship hardware wallet from Trezor and is based on the design of the highly popular Trezor Model T, albeit, with some upgrades. Uncover all the features of this wallet in our Trezor Safe 5 review.

Trezor Safe 5 Key Features
- Design & Durability: The color touchscreen, reinforced with Gorilla Glass 3, is a standout feature, offering a smooth, scratch-resistant display that’s built to last. The minimalist design is lightweight but feels solid, emphasizing practicality over showmanship.
- User Interface: Trezor’s Trezor Suite software is a dream for crypto purists. It integrates beautifully with the wallet, giving you full control over transaction details and privacy settings. It even supports Tor for added anonymity.
- Supported Cryptocurrencies: The Safe 5 supports over 9,000 assets (yes, you read that right), making it a fantastic option for anyone with a diverse portfolio. From major coins to lesser-known tokens, this wallet has you covered.
- Security Features: Built on Trezor’s open-source framework, the Safe 5 ensures that users can verify its security independently. The wallet also incorporates robust security features, including PIN protection, passphrase support, and recovery options that safeguard your secret recovery phrase like a digital fortress.
- Unique Features: Beyond its open-source credibility, the Safe 5 offers coin control, letting you decide which specific UTXOs (unspent transaction outputs) to spend, perfect for those who take privacy seriously.
- Compatibility: Works seamlessly across mobile and desktop platforms, integrating with popular tools like MetaMask and MyEtherWallet, while keeping your private key completely offline.
Trezor Safe 5 Pros and Cons
Pros
-
Open-source transparency ensures trust.
-
Color touchscreen with Gorilla Glass 3 for durability.
-
Supports over 9,000 cryptocurrencies.
-
Privacy-focused features like Tor support and coin control.
-
Lightweight yet sturdy build.
Cons
-
No Bluetooth or wireless connectivity.
-
Lacks staking and NFT management features.
-
No customization options like Ledger’s standby mode.
The Safe 5 boasts a beautiful design, compact size, and support for over 9,000 assets. It features a highly secure EAL6+ NDA-free secure element, marking a significant improvement over the older Model One and T versions. This advancement, along with the Trezor Safe 3, sets it apart from competitors like Ledger and ELLIPAL. The Safe 5 features a color touchscreen and is the most durable Trezor hardware wallet to date, thanks to the anodized aluminum body and Gorilla Glass touchscreen.
What to Do If You Suspect a Crypto Wallet Security Breach?
If you suspect your crypto wallet has been compromised, time is of the essence. Reacting quickly can be the difference between preserving your funds and losing them. Here’s what to do immediately if you believe your crypto wallet security has been breached:
Cease using the affected wallet. Avoid sending, receiving, or signing any new transactions. The more you interact with a compromised wallet, the more you risk further losses.
If you still have access and control, move your remaining crypto assets to a newly created, secure wallet, preferably one that uses a different device and a brand-new seed phrase. Use a hardware wallet or a trusted cold storage solution if possible.
Run a full malware and virus scan on your device. Breaches often result from keyloggers, clipboard hijackers, or phishing software. Consider wiping and reinstalling your operating system for full peace of mind.
If you use a browser extension wallet (like MetaMask), go to a site like revoke.cash and revoke any suspicious smart contract approvals that may be draining funds or monitoring wallet activity.
Immediately change passwords for any related accounts, including exchanges, email, and password managers. Enable two-factor authentication (2FA) where available, preferably using an authentication app rather than SMS.
If the compromise involved a centralized exchange or known dApp, notify their support team. They may be able to assist or at least monitor suspicious activity involving your wallet address.
Use blockchain explorers (like Etherscan or Blockchain.com) to track any outgoing or unauthorized transactions from your wallet. Document everything, it may help with recovery efforts or legal claims.
After the situation is stabilized, revisit your security practices. Consider upgrading to a hardware wallet, creating a better seed phrase backup system, and segmenting your wallets by use.
A breach is devastating, but it’s also a wake-up call. Strengthening your crypto wallet security after an incident can help ensure it never happens again.
Stop All Activity Immediately
Transfer Remaining Funds to a Safe Wallet
Check for Malware or Keyloggers
Revoke Suspicious Permissions
Change Passwords and Enable 2FA
Notify Relevant Platforms
Monitor Blockchain Activity
Educate and Secure Going Forward
Conclusion: Crypto Security
Crypto wallet security is one of the most important responsibilities for any digital asset holder in 2026. Just like you wouldn’t share your bank account number, you should treat your private keys and seed phrases with the same level of caution. Whether you’re storing coins on mobile devices, hardware wallets, or browser-based apps, protecting your assets requires strong passwords, strong encryption, and constant vigilance.
As the industry grows, so do the threats, from phishing to malware to fake wallet apps. Users must remain alert and proactive to prevent loss. Back up your seed phrases properly, avoid storing sensitive information online, and never share wallet credentials. By following the best crypto wallet security tips, you’ll reduce risk and better understand how to keep your cryptocurrency safe in a decentralized world. Remember, in crypto, you are your own bank. Security starts with you.
DISCOVER:
FAQs
Why is crypto wallet security so important?

Crypto wallet security is essential because it protects your cryptocurrency from hackers, phishing attacks, malware, and other online threats. Without proper wallet security, your funds can be lost permanently with no way to recover them.
What is the safest type of cryptocurrency wallet?

The safest type of crypto wallet is a cold wallet, such as a hardware wallet or a paper wallet, because it stores your private keys offline and is not connected to the internet, making it much less vulnerable to cyberattacks.
Are hot wallets safe?

Hot wallets can be secure for small amounts or frequent transactions, but they carry more risk due to their constant internet connection. For long-term storage or large holdings, cold wallets are a safer choice.
What are the main threats to my cryptocurrency wallet?

The most common threats include phishing emails, fake wallet apps, malware, keyloggers, clipboard hijacking, SIM-swapping, and improper seed phrase storage. These attacks often target users’ private keys and login credentials or trick them into revealing sensitive information.
How can I protect my crypto wallet against hackers?

Use strong, unique passwords, enable multi-factor authentication, and never share your private key or seed phrase. Store your seed phrase offline in a secure location and avoid accessing your wallet on unsecured networks or public Wi-Fi.
What is the difference between a private key and a seed phrase?

A private key is a cryptographic code that allows you to sign transactions from a single crypto address. A seed phrase is a series of 12–24 words that acts as a master key to generate and recover your entire wallet, including all private keys.
Should I store my crypto seed phrase digitally or physically?

You should store your seed phrase physically, not digitally. Writing it down and securing it in a fireproof safe or using a metal seed phrase protector minimizes the risk of theft or loss from online threats.
How do I know if my cryptocurrency wallet has been compromised?

Signs of compromise include unauthorized transactions, login attempts from unfamiliar devices, or changes to your wallet settings. If you suspect a breach, move your funds to a new secure wallet immediately and investigate the cause.
Can a cryptocurrency wallet be recovered if I lose the device?

Yes, most crypto wallets can be recovered using your seed phrase. This is why securely storing your seed phrase is critical. Without it, recovery is typically impossible.
References
- “The Basics about Cryptocurrency.” Oswego State University of New York, https://www.oswego.edu/cts/basics-about-cryptocurrency
- “Digital Currencies.” Reserve Bank of Australia, https://www.rba.gov.au/education/resources/explainers/cryptocurrencies.html
- “A Cybersecurity Guide to Safely Storing Your Cryptocurrency.” ECC University, https://www.eccu.edu/blog/cybersecurity/cryptocurrency-cybersecurity-how-to-store-your-crypto-safely/
- “Cryptocurrency Security Explained.” University of Tulsa, https://online.utulsa.edu/blog/cryptocurrency-security/
- Weaver, Nicholas. The Death of Cryptocurrency. Yale Law School, Information Society Project, 2023, https://law.yale.edu/sites/default/files/area/center/isp/documents/weaver_death_of_cryptocurrency_final.pdf
Why you can trust 99Bitcoins
Established in 2013, 99Bitcoin’s team members have been crypto experts since Bitcoin’s Early days.
Weekly Research
100k+Monthly readers
Expert contributors
2000+Crypto Projects Reviewed