Buying and Using Bitcoin Anonymously/Without ID
By: Alexander Reed | Last updated: 3/12/24
Are you looking to buy Bitcoin anonymously? Do you hate providing your photo ID to different Bitcoin exchanges? In this guide, I will try to answer all your questions about how to buy Bitcoin and remain completely anonymous when using it.
Buying Bitcoin Anonymously Summary
Despite its reputation, Bitcoin is not completely anonymous. With every transaction publicly disclosed on the blockchain and identity verifications required by many exchanges, it’s easy to see how your Bitcoin can be traced back to you.
There are methods to buy Bitcoin anonymously with cash, such as LocalCoinSwap or Bitcoin ATMs. Furthermore, there are places that require minimal identification and not necessarily your true identity, like Zengo, StealthEX, HodlHodl, or Bisq.

Lastly, to really get ‘off the grid’ and become completely anonymous, you will require solutions such as Tor and Tails, coin mixers, a VPN provider, and more.
The price for anonymity is usually inconvenient and vice versa. It is up to any user to decide how much they will sacrifice one for the other.
That’s how to remain anonymous in a nutshell. If you want a deeper explanation of the process, keep reading. Here’s what I’ll cover:
- Is Bitcoin Anonymous?
- 3 Easy Methods to Buy Bitcoin Anonymously
- Buying Bitcoin Without Verification/Photo ID
- Why Stay Anonymous?
- How to Use Bitcoin Anonymously (Basic Guide)
- How to Become Anonymous (Advanced Guide)
- Anonymizing Your Bitcoin
- Conclusion
1. Is Bitcoin Anonymous?
No, it isn’t. While Bitcoin is far more private than credit cards, it’s much less anonymous than cash.
The way Bitcoin works is that all Bitcoin transactions are stored in a public ledger called the blockchain.
The data stored in each of these transactions includes a Bitcoin transaction amount, the Bitcoin addresses of the sender, and the Bitcoin address of the recipient.
Can Bitcoins be Traced?
Because every transaction uses bitcoins from a prior transaction, and the blockchain is public data, every Bitcoin payment has a traceable history that anyone can view.
While cryptocurrency addresses are 100% traceable, they can’t be linked to a specific person or entity. That’s why Bitcoin is often called pseudonymous or pseudo-anonymous.
However, a person’s identity can be associated with a Bitcoin address through other means. For example, when people publish their name together with their Bitcoin address online (among other ways).
Once the association has been made, someone with enough determination, time, and resources could analyze the blockchain and determine how many bitcoins an individual has, how they receive them, and how they spend them. In other words – you can follow the paper trail (digital trail).
To use Bitcoin anonymously, precautions must be taken to prevent your true identity from being associated with your transactions and addresses.
2. 3 Easy Methods to Buy Bitcoin Anonymously
Method 1 – LocalCoinSwap
If you’re looking to buy Bitcoin anonymously, then the easiest way would be to buy Bitcoin with cash and in person, if possible. Use LocalCoinSwap to find someone near your location who is willing to sell Bitcoin for cash.

You can use an alias email address to sign up for LocalCoinSwap; their verification process is optional. When you use cash, it’s easy to become untraceable as there is no documentation for the transaction.
Remember that most sellers on LocalCoinSwap don’t like to deal with anonymous buyers; however, since you’re paying in cash, this should be less of an issue.
Method 2 – Bitcoin ATMs
Another way to buy Bitcoin anonymously is to go to your nearest Bitcoin ATM and buy it with cash. If you are in the US, try out one of Coinflip’s ATMs that currently offers 10% off the transaction fees if you are using the “99BTC” promo code.
Buying Bitcoin via an ATM is probably the best way to buy cryptocurrency anonymously; however, not everyone has an ATM nearby.
When asked to enter your Bitcoin address at the ATM, just specify that you don’t have one. This will generate a new paper wallet for you in most cases, and you’re good to go. Later, you can import the private key from that paper wallet and send those Bitcoins wherever you like.
Do I need an ID for a Bitcoin ATM?
Some Bitcoin ATMs require identification. If they don’t, they’re usually limited in the amount of Bitcoin you can buy.
Do Bitcoin ATMs charge a fee?
Yes. Most ATMs charge a fee (usually between 7% and 10%). If the fee isn’t stated explicitly, it’s “hidden” inside the exchange rate. Do your own calculations beforehand to have a rough estimate of what you expect to receive.
Method 3 – Prepaid Card
One way to stay anonymous is to use a prepaid credit card you can get at any supermarket or convenience store. You can then use this card to buy Bitcoin without the need to supply any form of identification through sellers on LocalCoinSwap.
3. Buy Bitcoin Without Verification/Photo ID
The following places allow you to buy Bitcoin without verifying your identity; however, they do not accept cash.
Zengo
Zengo is a great crypto wallet and exchange that offers users top-level security and privacy. Its unique keyless security system allows for anonymous and secure storage of cryptocurrencies.
With Zengo, users can buy crypto anonymously, i.e., without performing KYC. However, this feature will depend on which payment provider processes the order, the country involved, and the amount of Bitcoin bought.
Zengo also has the Zengo Pro subscription feature for $9.99 monthly, offering many additional features.
- Legacy Transfer allows you to pass your wallet on to loved ones.
- Lock your assets to a unique 3D FaceLock biometrics.
- Alerts and protections against Web3 attacks.
- Priority support is guaranteed in less than 1 hour, with most responses handled in less than 5 minutes.
Read our full Zengo review here.
HodlHodl
HodlHodl is a global P2P Bitcoin exchange that allows users to trade directly with each other. The site doesn’t hold users’ funds, which allows it to avoid KYC and ID verification processes.
HoldHold locks user funds in multisig escrow, which minimizes the possibility of theft of Bitcoin assets and reduces trading time.
Bisq
Bisq is open-source, peer-to-peer software that allows you to buy and sell cryptocurrencies in exchange for national currencies. No registration is required to use Bisq.
Bisq does not hold any bitcoins. Much like HodlHodl, all cryptocurrencies are held in multi-signature addresses rather than in a Bisq-controlled wallet.
Additionally, Bisq does not hold any fiat currency (i.e., dollars and euros). Fiat is transferred directly from one trader to the other.
StealthEX
StealthEX is a cryptocurrency platform that offers asset swaps and direct sales with debit and credit cards. What’s noteworthy about StealthEX is that the platform doesn’t require users to sign up. There is no KYC; swaps and purchases can be accomplished without registration.
The exchange has over 1,400 coins available for swapping. For direct crypto purchases, StealthEX accepts Visa, Mastercard, Google Pay, and Apple Pay.
StealthEX is also a custody-free exchange, meaning they don’t store user funds. StealthEX locates the best deal during a crypto swap and makes the swap between wallets for you. There are no extra or hidden fees, but you must pay the network transaction fee for every exchange.
4. Why Stay Anonymous?
Before we discuss ‘how to stay anonymous,’ we need to understand why it is important to become anonymous in the first place.
The main reason most often is that you don’t want to get hacked or become a potential target. Raising your privacy level will lower your risk of falling victim to such actions. Some people value privacy as a matter of principle, while others lean into Bitcoin’s anonymity and privacy features for more specific activities, like accessing the darknet, possibly, but not necessarily, for illicit activities.
However, not all examples point to “bad intentions” or paranoia; the anonymous and private aspects of Bitcoin also lend themselves to, for example, the online gambling industry. Because anonymity and privacy are at the very backbone of Bitcoin, many online crypto casinos require very few personal documents (like IDs, passports, utility bills, etc.) to register and play.
Furthermore, anonymous transactions allow people to make private donations—like to political parties or public causes—without exposing their real identities. This is especially useful if you want to support a political party or a cause without facing public scrutiny.
Bitcoin’s blockchain is built on rock-solid cryptography, preventing counterfeiting and other types of fraud, but the human element in Bitcoin transactions is always the “weakest link.”
Using an online pseudonym (e.g., Satoshi Nakamoto) will improve your privacy, but remember that a capable investigator can identify you over a standard internet connection.
Most Bitcoin wallets broadcast your real IP address, which can then be easily associated with your address(es).
As all Bitcoin transactions are a matter of public record, any address that becomes associated with your identity reveals four important pieces of information:
- How much Bitcoin you have or had in that address
- Exactly when you receive Bitcoin
- Who you receive or received that Bitcoin from (unless they employ effective privacy methods)
- The address to which you send any Bitcoin (which, as with Number 3, may identify its owner).
Bitcoin wallets with coin control features allow you to make payments from select addresses (technically called UTXOs), giving you some control over what addresses you expose.
However, the way most Bitcoin wallets handle change often results in various addresses within the wallet becoming linked.
As a result, one identity-associated address under your control can “leak” information about your other “unknown” addresses.
5. How to Use Bitcoin Anonymously (Basic Guide)
As I already suggested, you can assume, as a starting point, that all addresses within your Bitcoin wallet can be linked to your real identity somehow.
If you’ve bought coins from an exchange with identity verification procedures or done business under your real name, this is quite possibly the case.
The good news is your privacy can be partially or fully recovered from this state.
Improve Bitcoin Privacy
Avoid reusing addresses whenever possible. Generate a new address for each transaction you receive. Generating wallet addresses is free, so it’s an easy anonymizing step.
While there’s little point in updating a static address associated with your identity, such as a Bitcoin tip (donation) address linked to a social media profile, this is recommended practice in most other situations.
It’s best to use HD wallets, which allow a virtually unlimited number of addresses to be linked to a single private key.
Improving Your Online Privacy
If you browse the internet from the same computer or device you use for Bitcoin, you should definitely upgrade your privacy and security features.
The information site Prism-Break provides a variety of recommendations for different operating systems and devices.
At a minimum, consider installing ad and JavaScript blockers, as well as denying or regularly clearing cookies. HTTPS Everywhere is also recommended to encrypt and secure online browsing.
Another option is to use an end-to-end encrypted email service such as Mailfence, which protects your data from third parties and governments.
Remember – mature and open-source solutions are usually preferable when selecting privacy/security/encryption software.
Avoid SPV and Hosted Wallets
SPV wallets do not store the blockchain locally. Instead, they query a single SPV server for transactions involving your wallet’s addresses.
While this functionality is far more efficient and fast than parsing the blockchain locally, the trade-off is that every Bitcoin address you own is submitted to the SPV server.
Almost all SPV wallets (also known as thin or light wallets) leak the addresses you own to whatever SPV server they connect to.
Some SPV wallets can use bloom filters to help conceal which addresses you own by requesting extra transactions that don’t involve your wallet.
Electrum, for example, doesn’t use bloom filters at all, so any server you connect to knows every address that you own. Another great privacy-focused wallet you can use is Incognito Wallet, an open-source wallet that enables privacy on any asset it holds. The wallet applies anonymity techniques like RingCT and StealthAddress (similar to Monero) – to all assets it supports. This includes Bitcoin, Ether, USDT, and hundreds of other cryptocurrencies.
Hosted clients (wallets managed by a third party like Coinbase) are even worse regarding anonymity. All of your private and public keys reside on third-party servers, so it is trivial for the operator to know which Bitcoin addresses you own.
Additionally, any other information you’ve submitted to the service is associated with your Bitcoin addresses and can be easily accessed by the service’s operators.
These types of wallets make it easy for an SPV server operator or service administrator to know which Bitcoin addresses you own and associate them with your IP address.
If the operator is subpoenaed or NSL’d to provide logs to law enforcement or government agencies, he or she could potentially leak the information, lose it, or expose it.
One of the fundamentals of Bitcoin is not having to trust any single party. In terms of anonymity, it’s best to use a full Bitcoin client like Bitcoin Core or Armory and store the entire blockchain locally.
Managing Passwords
Human-memorizable passwords tend to be weak. This problem and its solution are best demonstrated by the following XKCD webcomic:
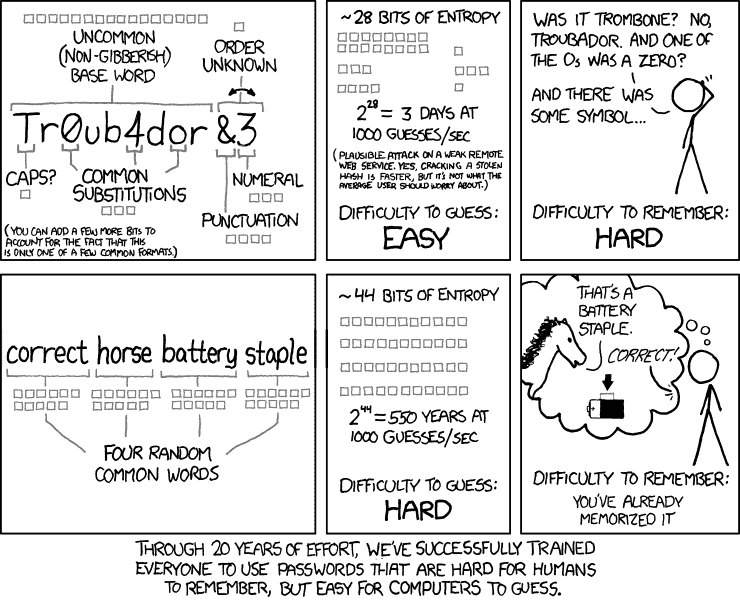
Using your own variant on “correct horse battery staple” for multiple accounts is also a bad idea from a security and privacy perspective.
A single compromised account could leak all the passwords to your email, Bitcoin exchange, and other sensitive accounts. Trying to memorize a different password for tens or even hundreds of accounts is similarly a recipe for disaster.
The solution is to use a good, random-word password and a password manager. Password managers generate strong, lengthy, random passwords you don’t need to memorize.
The program stores your passwords in an encrypted format. They are accessible only when you enter your single master password into the manager (which should be memorized and never written down).
6. How to Become Anonymous (Advanced Guide)
Online security is often characterized as a trade-off between effectiveness and convenience. You can choose which end of this scale you wish to be on.
In this chapter, I’ll review methods that require more effort but make your steps much less traceable.
Disguising Your IP Address with Tor
The first step in becoming anonymous is using Tor, a powerful anonymity tool.
Visit TorProject.org to download and install Tor (short for The Onion Router). Once activated, Tor opens as a separate, Firefox-based internet browser that disguises your IP address.
Tor works by routing your connection through several other participating computers. The ultimate effect is that whichever website you access will see your request as coming from an entirely separate machine, usually in a different state or country.
Although it masks the IP address and certain potentially identifying browser characteristics, Tor is by no means a complete privacy solution.
Using your real name, accessing your regular email, or signing into social media via Tor will have exactly the same de-anonymizing effect as doing so through a regular browser.
For a more private email address, create a dedicated darknet email account for Tor usage, such as a Mail2Tor account.
Note that Tor also disables JavaScript by default; certain websites won’t load properly without JavaScript, but re-enabling it can potentially de-anonymize.
Once browsing through Tor, you may also access the darknet further to research internet anonymity without undue concern over prying eyes.
Running Bitcoin Through Tor
Once you feel familiar enough with Tor, it’s time to make your Bitcoin addresses anonymous. To do that, you need your wallet to connect through Tor.
One solution can be using Bitcoin Core, which automatically connects through Tor if it detects its presence.
To force this behavior, follow these instructions on Bitcoin’s GitHub. Most other wallets can also connect through Tor; consult their documentation to discover how.
Consider installing a new wallet that only ever connects through Tor. To do that, disable your internet connection and configure the new wallet to run exclusively via Tor before launching it. You may then re-enable your internet connection and allow the wallet to sync.
If using a full wallet, copying an existing blocks folder (ensure that you don’t also copy your wallet.dat folder) to the “Tor wallet’s” data directory will greatly speed up the syncing process.
Directly transferring bitcoins from your old wallet to this new one will somewhat obscure the ownership of those coins. However, far more sophisticated transferal methods (covered later) will be more effective at disguising this flow of funds.
Consider Using a Virtual Private Network (VPN)
As mentioned, Tor does not guarantee 100% privacy. An adversary who owns both the first and last machines you connect through will see your IP address and the sites you access.
If you’re willing to pay for a little extra peace of mind, consider a VPN service. Instead of accessing the internet – or Tor – directly, your connection will be routed through the VPN’s servers.
A VPN has somewhat similar benefits to Tor; it obscures your IP address. In fact, most VPNs allow you to spoof the nationality of your IP address (which can be helpful for accessing location-specific data).
VPNs also provide security benefits. They act to screen your device for malware via firewalls and proxies.
Unlike certain sites that block access from known Tor routes, VPNs usually afford unlimited access and much higher bandwidth than the Tor network.
It’s entirely possible to access Tor through a VPN for another layer of obfuscation.
Disk Encryption
Leaving traces of your activity on your hard drive or removable media represents another way in which anonymity may be compromised. Disk encryption software allows you to encrypt a file, folder, or entire drive such that it can no longer be accessed without a password.
Encrypting your Bitcoin wallet file and any sensitive information stored on your computer is good practice. With decent disk encryption software, you can create multiple, secure backups of your most important files and data and disperse them on USB memory sticks and the like.
Wikipedia offers a good comparison of the available disk encryption software options. Do not rely on the Windows BitLocker program; unlike open-source alternatives, it is not provably secure.
Warning: If you lose or forget your encryption password, you’ll lose access to any encrypted files. No recovery!
The Amnesic Incognito Live System (TAILS)
Finally, if you’re serious about your privacy, you’ll want to bring all the above methods together in a secure operating environment. Unfortunately, standard operating systems do not prioritize privacy.
Windows, for example, is known for its efforts to monitor users. It, therefore, makes sense to boot into a secure, privacy-respecting operating system before attempting to send Bitcoin anonymously.
The best possible option here is Tails, a variant of the Debian-based Linux operating system, which by design leaves no trails.
Don’t worry if you’ve never used Linux before; Tails features an interface that will be familiar to any Windows or Mac user. Tails can even mimic the appearance of Windows so that casual onlookers won’t notice anything unusual about your computer usage.
Tails packs a host of privacy, security, and encryption features into a package small enough to fit on a portable USB drive. It even includes KeePassX (a password manager) and the Electrum light Bitcoin wallet as standard!
To boot to Tails on start-up, the USB drive must be formatted as bootable via a program like Universal USB Installer or Rufus.
Tails must then be downloaded and installed on the drive. Note that installing and keeping Tails updated will require 2 such USB devices.
If you want to get started with Tails, you can use this simple online tutorial.
Altering your Bios setup to booting from Tails rather than the hard drive allows you to securely use untrusted computers and networks.
This means you may anonymously send Bitcoin from even a public, monitored computer, such as those in a library or internet café, without leaving any traces of your identity or activity.
While Tails easily defeats any software-based data logging, it can’t protect against hardware keyloggers or hardware screen captures. Fortunately, Tails contains a virtual keyboard and other mouse-driven text entry applications.
For password entry on untrusted devices, employing a combination of onscreen text-entry and spam-text logging countermeasures is recommended.
Tails stores no information regarding the software you use, sites you visit (via its built-in Tor browser), or anything else. However, Tails does allow you to create an encrypted, persistent volume within your USB stick.
Any data placed in the persistent volume will be maintained between sessions. It’s advised to store your password manager data file within this volume.
7. Anonymizing Your Bitcoin
If you have bitcoins that have already been in some way tainted with a link that could identify you, it’s possible to break that link and effectively anonymize the coins again.
If done correctly, future transactions from that point forward won’t be connected to you anymore.
Tumbling Coins Through Mixers
For anonymizing purposes, there are mixers (also known as tumblers). The basic concept is that you send the coins you want to have anonymized to the mixer, which in turn sends back the same amount minus a fee to a new address you provide.
The coins you receive back are from a large pool maintained by the mixing service and should ideally have no connection to your original coins.
The major flaw of this concept is its centralized nature. You have to trust the mixing service to return your coins, and additionally, you have to trust that they do not keep any records of the mixing transactions that were performed.
The latter point is especially tricky since you can never know for certain what they are doing with the data. If the mixer doesn’t keep any transaction records, they cannot prove it.
On the other hand, you have no way of knowing if they don’t or are even forced to hand over their data.
JoinMarket, an implementation of a privacy-improving technique first proposed by core developer Greg Maxwell, offers a trustless, decentralized method of mixing.
This infographic provides a gentle introduction to the workings of JoinMarket. Although a fairly simple concept, at the present state of development, JoinMarket represents a more complicated undertaking than sending coins through a mixing site:
If you have a good understanding of Bitcoin and you’re prepared for a more hands-on method, JoinMarket is highly recommended.
JoinMarket gives you back control over the mixing process and lowers your risk and transaction fee. It even lets you earn a little money by helping others mix their transactions.
Another easy way to implement coin shuffling is to use the Wasabi wallet. This is an open-source wallet that implements trustless coin shuffling with mathematically provable anonymity.
Obscuring the Trail Through Altcoin Shifting
Why stop at mixing between Bitcoin addresses? Mixing between Bitcoin and privacy-centric altcoins provides another layer of obscurity.
This method may require a little less trust than a centralized mixing service. The best altcoin to use for this purpose is probably Monero (XMR).
This short guide covers buying Monero with Bitcoin (tl;dr, you can use Binance). To anonymize your bitcoins, simply convert them to XMR, forward them to a new Monero address under your control, and then convert them back to a new, anonymous BTC.
Circling Bitcoin Through an Exchange
This is perhaps the easiest method, but it doesn’t provide 100% total anonymity. If you have an account on a crypto exchange like Coinbase, Binance, or Kraken, you can send your Bitcoin to the exchange and then withdraw it to a different wallet address than the one you sent it from.
This works because many exchanges have a general “pool” receiving wallet that assigns incoming coins to your exchange account. You can then send them to a different address.
Whichever exchange you use will be able to see where you sent it, but from the outside, it will look like X sent 0.025 Bitcoin into “Binance Wallet 4.” That’s it. A future withdrawal will come from one of their general wallets. They will know, but again, the outside won’t.
8. Conclusion – Anonymity Comes at a Price
To sum up, it’s up to you to decide how much anonymity you need online. The more anonymous you want to be, the more effort you’ll need to navigate around the web.
This guide provides you with the main tools and techniques so you can mix and match whichever works best for you.
If you’re just looking to buy a few coins without being traced, just use cash – it will solve most of the issues. If you are just concerned with providing your ID, there are ways to bypass that too.
However, if you want to get really serious about using Bitcoin anonymously around the web, you must go through the trouble of becoming truly and fully anonymous.
If you’ve had any experience with buying Bitcoin anonymously, I would love to hear it in the comment section below – don’t worry, you can use an alias 🙂





Could you send a fiat bank transfer to your KYC exchange, then convert fiat to USDT. Send USDT payment to a seller on Hodl Hodl (or similar P2P marketplace), receive purchased BTC to a fresh new address?
Your exchange would know you bought and transferred USDT to an external address, but could anyone tie the BTC to you?
CoinCorner registration require KYC verification after initial registration, and a few clicks on their APP. Totally BS.
I’ve been dealing with anonymity, go around, bypass all these thingy, since before the Silk Road. And yes, to explain it, in my experiences, mostly,
People with knowledges in variety, of, advanced, programming, languages, and, practically doing it, some use the term “playing with console or terminal”, as it’s totally different than doing coding or programming, which not a lot of people like that, if you get what i mean, and if you know one, chances are these are the kind of lot(s) of curiosities and error(s) solvers people.
So read that back few times to digest, because i understand how complicated it is, but, as a system engineer, and some very few individuals ‘will’ say, PLEASE NOTE, THE STATEMENT IS ONLY FOR SPECIFIC KIND OF PEOPLE, “complicated are excuses for weak minded people”.
So not to get confused, by specific, one simple example I can give, an international level or world class competitive fighter in class A, not B, and most definitely not class C. There’s a reason why I don’t use UFC.
Okay back to what I tried to say, not explain, it is difficult to make it easy to go through all these trouble, and yes, great power comes with great responsibility and sacrifices. So to the author, what you wrote, nothing is wrong, just mostly true.
I would suggest, for people who, just starting with BTC, and also who about to start or understand why anonymity, first, do a research about history of Silk Road in the Darknet. I believe there’s a documentary movie titled “Dark Web”. The reason is, if you really serious, you will watch, and understand, until the end, then you might reconsider about this. You’ll learn a lot from there, and also probably understand why I’m writing too much like wasting my time. No reason to explain, that’s all I have to say. I guess for US citizens, probably know about this thing
da fuq
That option clearly stated to set up a skype number using anon email.
My strategy:
bank –> Binance.us –> zecLite — (shielded transaction) –> Nighthawk –> no-kyc bibox account –> trezor
Just here to say that this article is misleading. I just tried the Coinflip ATM (“Method 2”) and it is *NOT* anonymous… it requires a mobile phone # and does not give the option of a paper wallet. Update your site man or take the guide offline!
Thanks, we’ll see about updating that.
There are several pubic mobile phones accesible from internet that people use to get sms codes anonymously (and publicly)
They will not accept these sms codes. Tried x3. Must use a real phone number. Or purchase an anon one with crypto.
use a burner