Following the attack that targeted the famous Italian spyware firm Hacking Team, documents leaked by the perpetrators show that the company was using a controversial Bitcoin wallet tracker.
The hack has proven that the Milan-based digital firm enabled its clients to hack computers and steal private information through a number of programs, apps and exploitation software that affected around 6,550 individual devices around the world.
 Take the example of the Bitcoin wallet tracker developed by Hacking Team that was compatible with Mac OSX, Linux and Windows.
Take the example of the Bitcoin wallet tracker developed by Hacking Team that was compatible with Mac OSX, Linux and Windows.
This software allowed the company to view and track different cryptocurrency transactions, specifically Bitcoin and Litecoin.
The company is mainly known for its Remote Control System software. The spyware enabled Hacking Team’s clients to monitor activity on a computer, allowing the users to capture files and email, record sound using the microphone and even track the position of the device, among other possibilities.
According to the documents, Hacking Team was working with United States agencies like the FBI (Federal Bureau of Investigation), the Department of Defense and the Drug Enforcement Agency (DEA). However, the leaked data also shows the company has been using malware and vulnerabilities to gain access to target’s networks and sell information to repressive regimes like Saudi Arabia and Russia, something Hacking Team previously denied doing.
The group Privacy International said that the recent “leak of materials reportedly shows how Hacking Team assisted some of the world’s most repressive regimes – from Bahrain to Uzbekistan, Ethiopia to Sudan – to spy on their citizens.
“We know from investigations by Citizen Lab that these tools are used to target human rights activists and pro-democracy supporters at home and abroad. Surveillance companies like Hacking Team have shown they are incapable of responsibly regulating themselves, putting profit over ethics, time after time. Since surveillance companies continue to ignore their role in repression, democratic states must step in to halt their damaging business practices.”
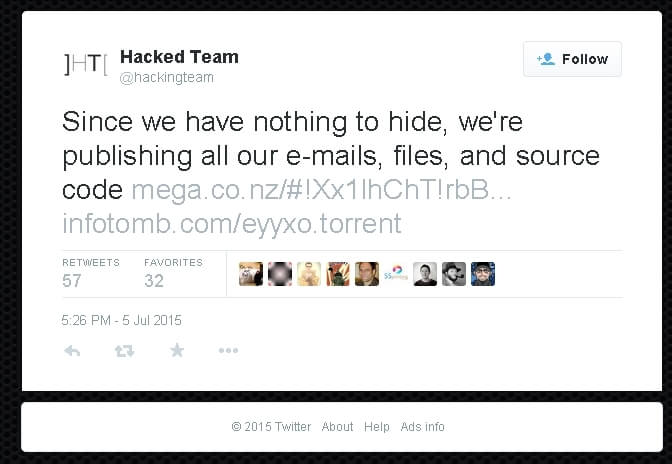
After the hackers shared the stolen data, Hacking Team’s employee Christian Pozzi took to Twitter to accuse the perpetrators of spreading “false lies.”
“A lot of what the attackers are claiming regarding our company is not true. Please stop spreading false lies about the services we offer. We are currently working closely with the police at the moment. I can’t comment about the recent breach,” Pozzi wrote before deleting his Twitter account.
Although it has been impossible to independently verify the veracity of the documents, digital security experts that have been analyzing the files have already identified massive exploits perpetrated by Hacking Team.

 No Comments
No Comments