The Chinese Bitcoin exchange BtcChina was hit by a massive DDoS attack (distributed denial-of-
The attack went on for nine hours on September 24 and no amplification techniques were used, according to The Hacker News, unlike what happened back in March, when the first DDoS attack of 300Gbps happened due to a DNS Reflection Amplification. In this case, the “victim” was Spamhaus, a Dutch anti-spam group.
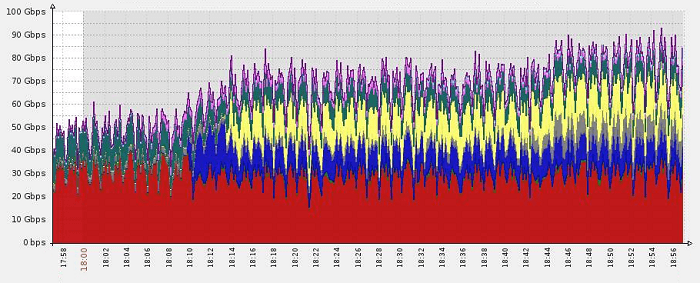
BtcChina was assisted by the cloud-based security company Incapsula, which helped the Chinese exchange to avoid the consequences of an attack with this magnitude. In the meantime, the firm made this graph public via Twitter with the message “we prevented a ~100Gbps DDoS. The attack’s load was distributed across our 350Gbps network”.
According to an expert at Incapsula, quoted by The Hacker News, “the attack against BtcChina took the form of a SYN flood rather than the DNS amplification-style attack. The attacker balanced the assault between small, high frequency SYN packets, and large, low-frequency SYN packets”, adding that “this amount of firepower isn’t cheap, or readily available, signifying a big step up in resources pulled together to launch this type of attack”.
After Incapsula’s intervention during the attack, the consequences of the assault were minimized. According to Marc Gaffan, the co-founder of the company, “the attackers either ran out of resources or money. It’s also possible they gave up after they realised they were not making headway”.

 2 Comments
2 Comments

Comments are closed.